Technologies
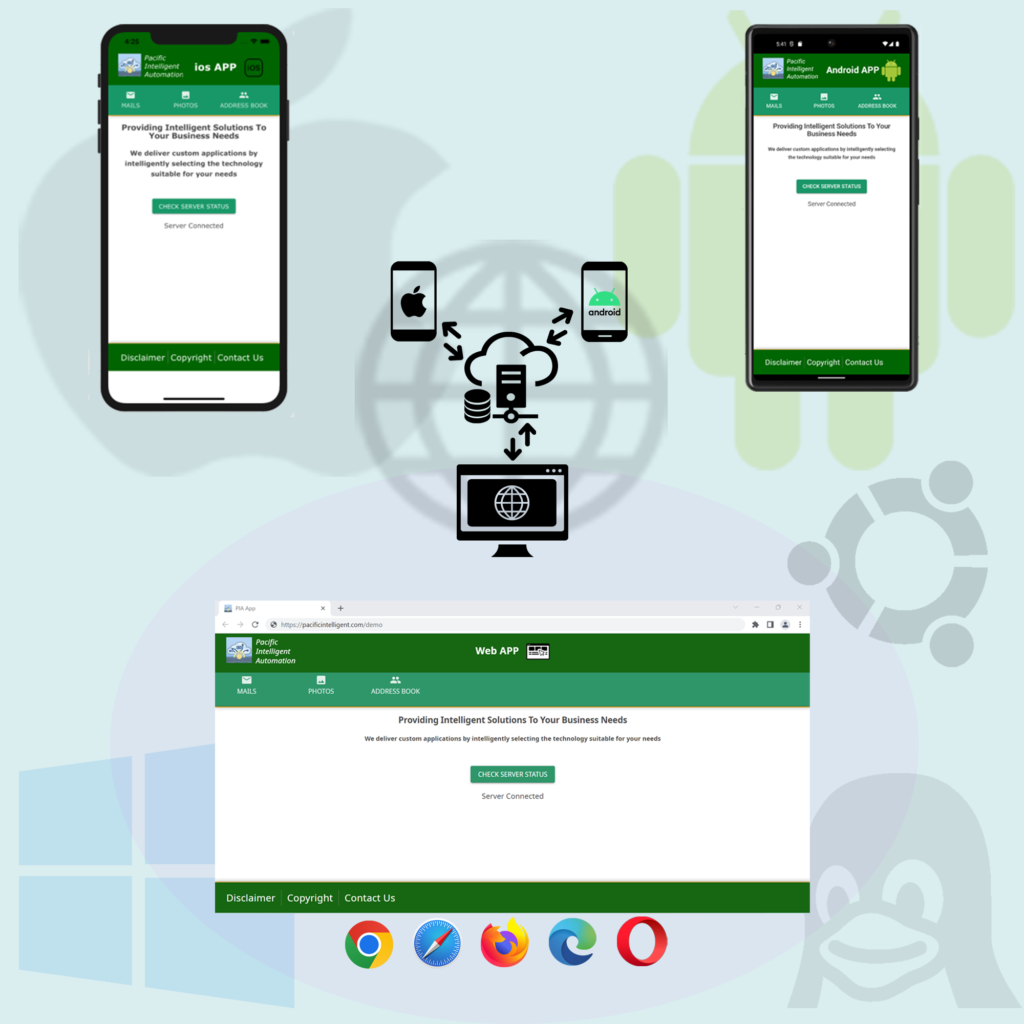
All-in-one Solution for Cross Platform and Web Applications
We develop applications that seamlessly run across multiple platforms, including PC, mobile phones and tablets, ensuring compatibility with various browsers and both iOS and Android devices.
By making your application available on the Google Play Store and the App Store, as well as through a responsive web page. We maximize your product’s reach, allowing you to engage a broader audience and enhance user accessibility.
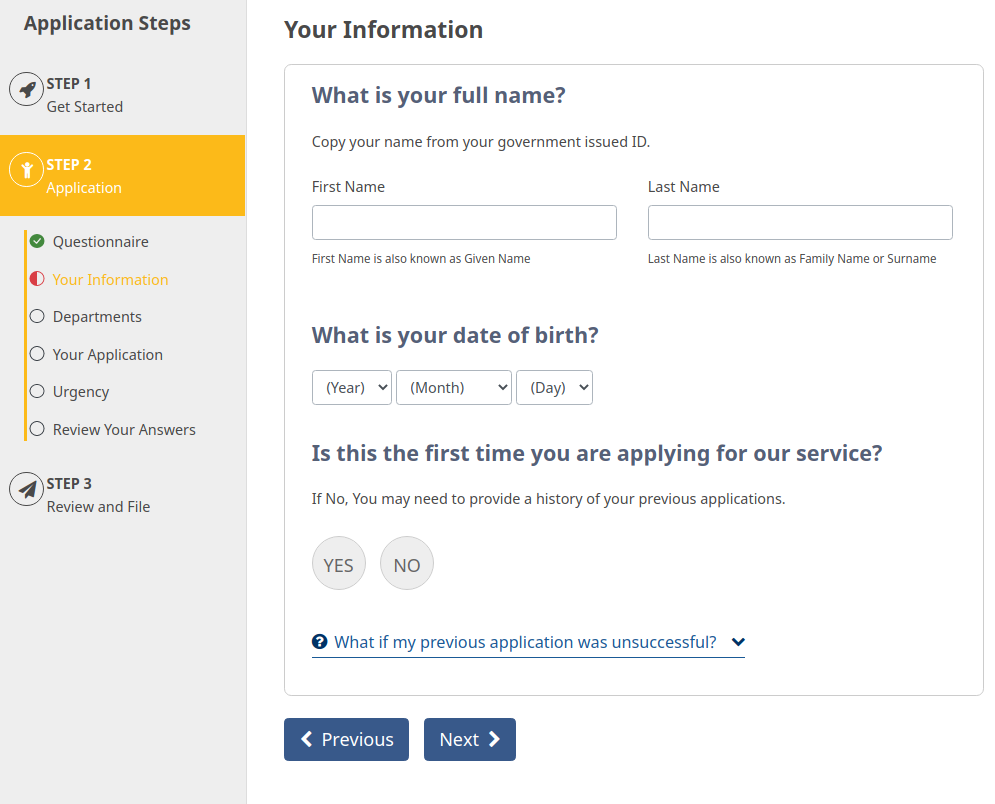
Survey-Based Applications
We develop survey-based applications that streamline user interactions and enhance customer experience. By answering a few simple and intuitive questions, your users can receive tailored results while the application handles complex calculations or dynamically generates sophisticated forms on their behalf.

PDF Generation
We offer robust PDF generation capabilities, allowing you to create and print elegant, professional PDF documents. If required, these PDFs can be made fillable, enabling clients to complete and sign them electronically.
Additionally, we provide the option to integrate QR codes into your PDFs, eliminating the need for manual data entry and streamlining document processing.
All PDF files and QR codes are generated within your secure environment, ensuring that sensitive information remains private and confidential.
Here is a sample of a generated PDF.
Elevated User Experience
We prioritize high-quality user experience throughout our development process, ensuring that your application is intuitive, accessible and engaging. Our approach to delivering an elevated UX includes:
- Maintaining consistency in user flow for seamless navigation.
- Providing easy-to-use components that enhance usability.
- Incorporating user feedback to refine and optimize the experience.
- Making different elements visually distinct for clarity and accessibility.

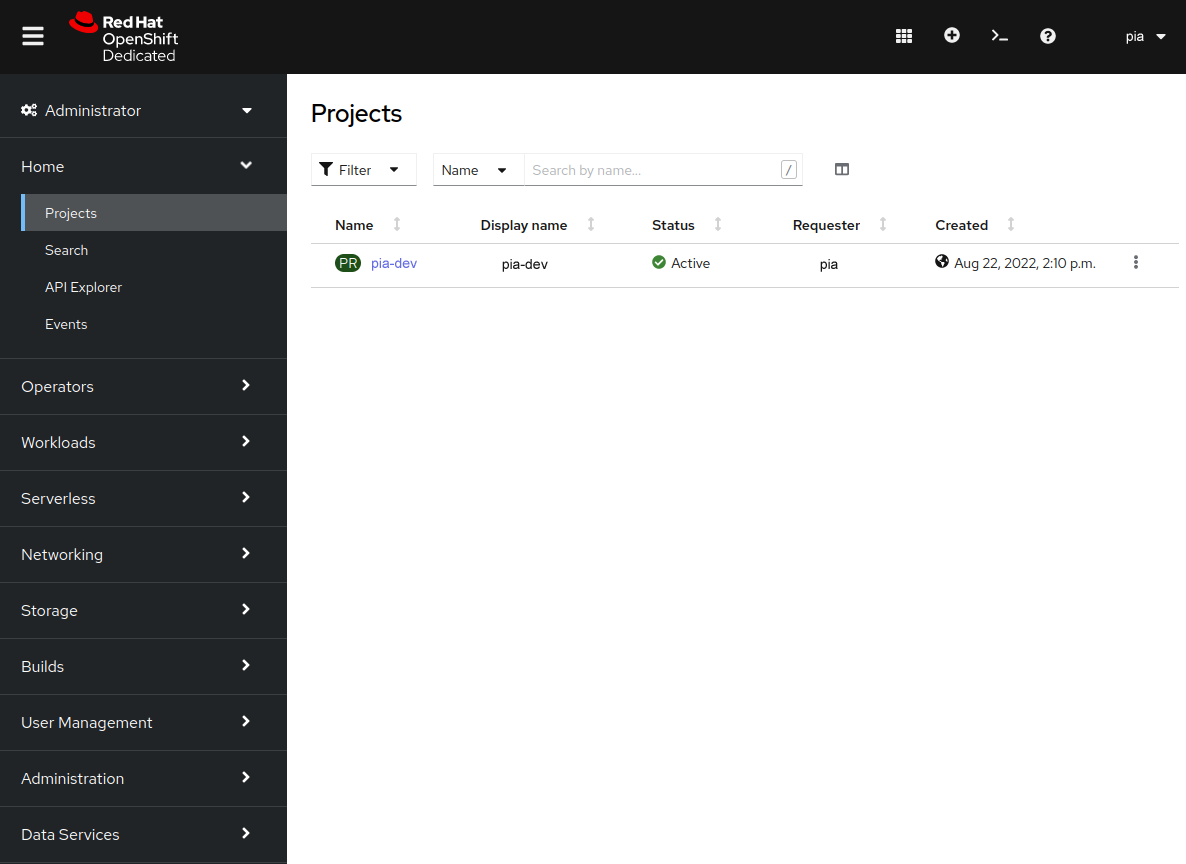
OpenShift Container Platform
We leverage the OpenShift Container Platform to automate Continuous Integration/Continuous Deployment (CI/CD) pipelines, ensuring a seamless and iterative development process.
Our approach enables:
- Efficient Feature Implementation: Changes are introduced through code updates.
- Local Testing: Developers validate changes before pushing them forward.
- Automated Deployment: Code changes are pushed to GitHub, triggering an automated CI/CD pipeline.
- Real-Time Client Feedback: Updates are deployed in the development environment for client review.
- Seamless Production Releases: Once approved, the same CI/CD process deploys the final solution into production.
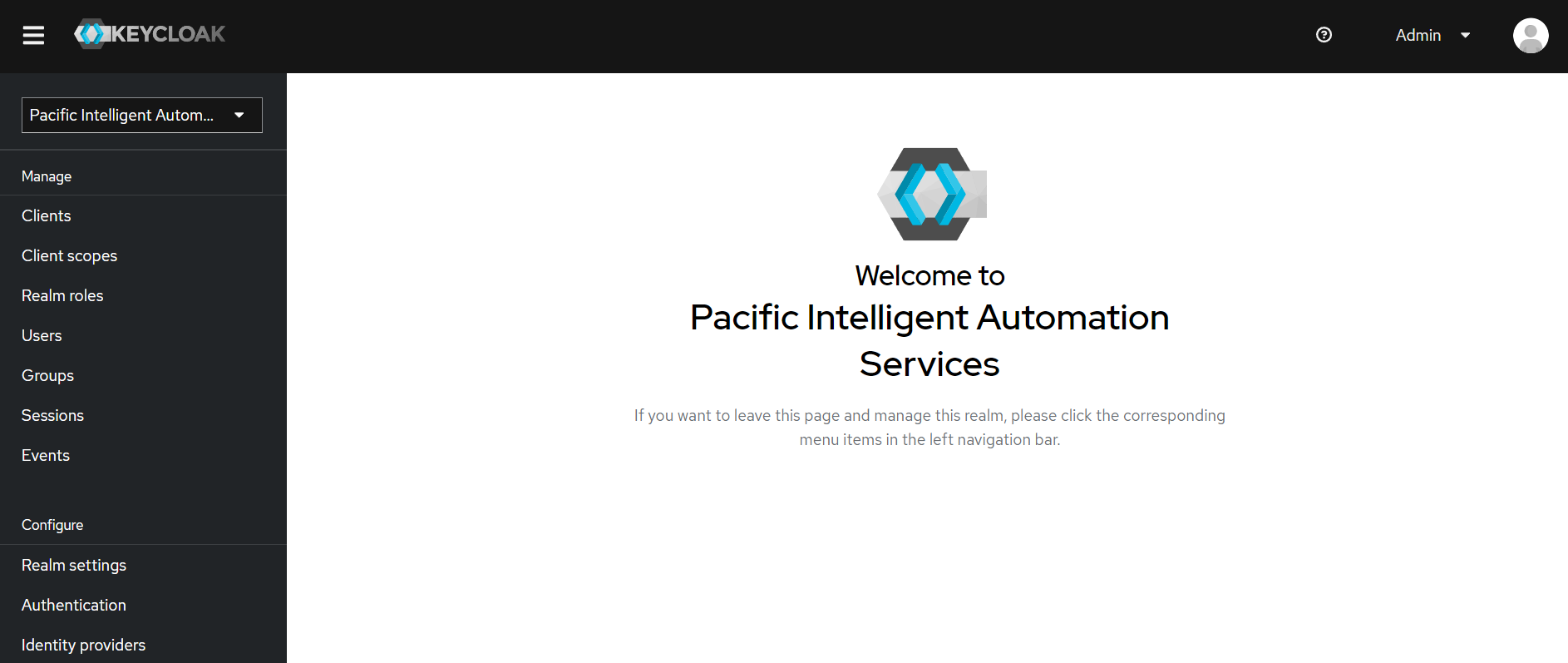
Keycloak identity and access management solution
We leverage Keycloak for Single Sign-On (SSO) authentication, simplifying user access and security management. Keycloak enables:
- Streamlined Access Control: It provides an easy and secure way to manage different user groups, ensuring that only authorized users can access specific resources.
- Role-Based Permissions: Once authenticated, users are assigned permissions by the application’s admin. These permissions determine the data and actions each user can access or modify, ensuring compliance with security policies and organizational roles.

More reliable and Secure applications
We offer a range of security features to enhance the reliability and protection of your application:
- Client Authentication: Securely authenticate your clients to ensure only authorized users can access your services.
- Role-Based Access Control: Admins can assign specific access levels to users, providing granular control over who can perform certain actions.
- Securing API Calls: Protect your REST APIs using cookies and tokens, ensuring secure communication between clients and servers.
- Data Encryption: Safeguard sensitive data stored in your database through encryption, reducing the risk of data breaches.
- Secure API Key Management: Store third-party API keys as secrets in OpenShift, preventing unauthorized access and misuse.
- Traffic and API Access Limitation: Limit API access and restrict outside traffic to your backend to block potential security threats.
- Audit Tools: Integrate audit tools into your application to track user activity and detect any suspicious behavior.
State of the art technologies
We are committed to using the latest, most stable tech stacks to build your solution. Our team prioritizes adopting packages with minimal vulnerabilities and exposures (CVEs) to ensure your solution maintains the highest levels of security and reliability.